Trusted. Sharp. Accountable.
Optimising Security Stacks.
Holding Vendors To Outcomes.
"like most large enterprises we had gaps as well as underperforming tools in our stack. inefficiencies compound so do efficiencies. observer solutions have helped us lean in to realise exponential posture enhancement without budget uplift"
ho Cyber defence - global 500
What We Do
At Observer Solutions, we help you:
Cut stack waste
Fix vendor drift
Deliver real outcomes
No fluff. No noise. Just results.
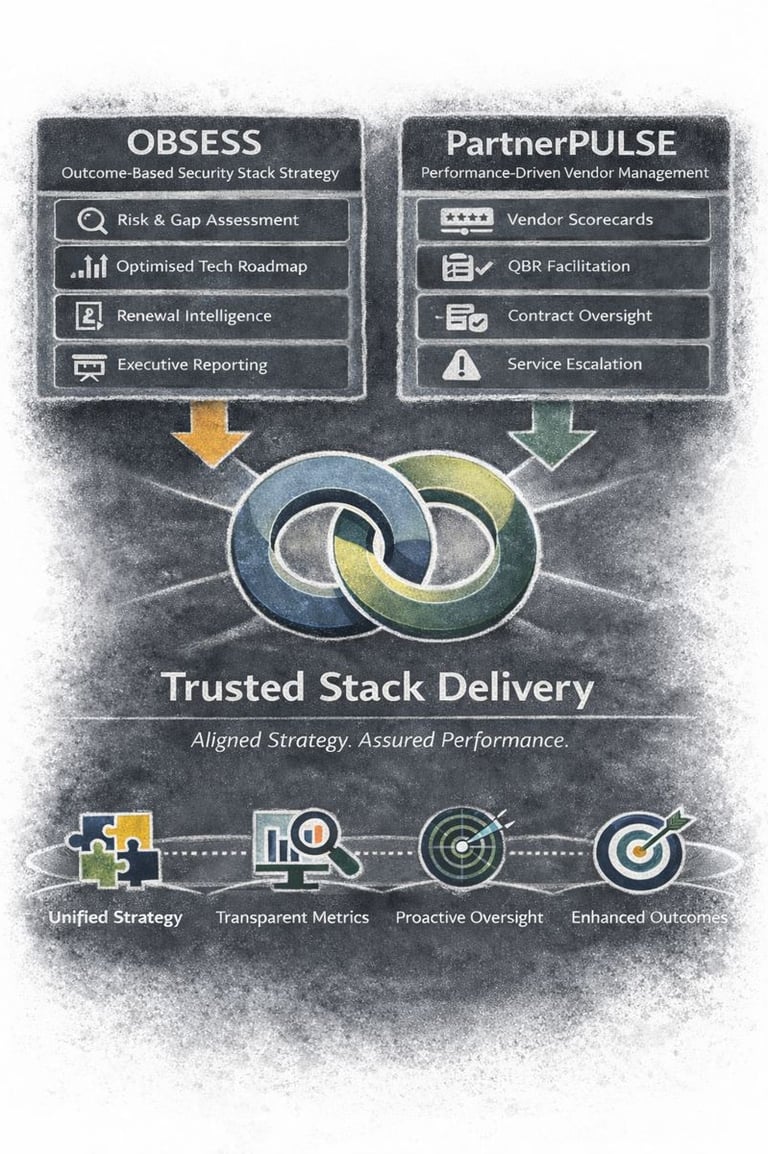
We deliver through our Trusted Stack Delivery model that comprises two pillars:
OBSESS and PartnerPULSE

>2,000
15
Approved For Partnership
Vendors Assessed


Pillar 1: OBSESS
(Observer Security as a Service)
Your stack. Aligned. Measured. Controlled.
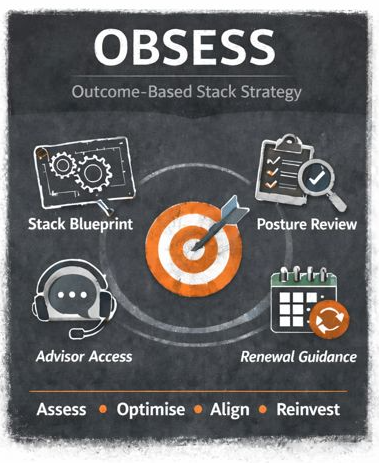
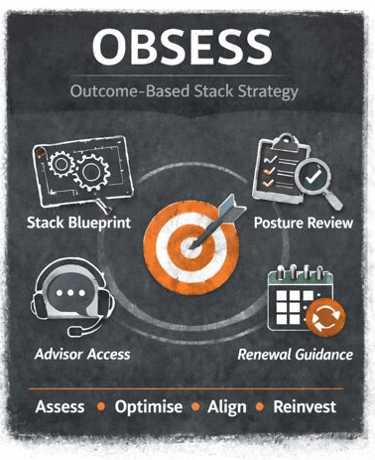
Our Premium Structured Advisory Service
Designed to help security leaders:
Reduce stack bloat and overlap
Plan smarter renewals
Align spend to risk and policy
Track outcomes from tool decisions
Access insight trusted by peers across sectors
It’s not consultancy. It’s not resale bias.
It’s clear, evidence-led strategy embedded into your cyber program.

Pillar 2. PartnerPULSE
PartnerPULSE can be Deployed alongside or independently of OBSESS.
It formalises how we:
Track vendor performance
Measure follow-through
Share market signals
Influence renewal and roadmap decisions
More than reporting. We’re in the room, on your side, making sure vendors deliver.
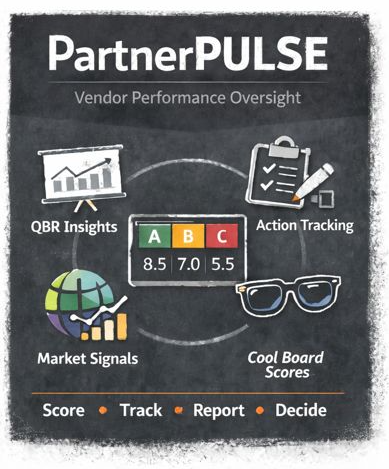
Our Vendor Accountability Framework.
CLIENTS
We don’t: sell hours
We don’t: push product
We do: move the needle — by helping cyber leaders buy better and hold vendors to outcomes.
Outcome-driven support for cyber leaders who expect more.
We'd love to hear from you:
VENDORS
Deliver better. Be rated. Stay relevant.
We review vendors for possible inclusion in our preferred portfolio.
Please first check you are in our ball park using the Vendor Standards button here:
sales@observersolutions.com
© 2026. All rights reserved.
